Last Updated on May 7, 2026 by Narendra Sahoo
PCI DSS controls are no longer just a compliance checkbox — they’re a mandatory security baseline that stands between your customers’ card data and sophisticated cybercriminals who are faster, smarter, and better-funded than ever before. According to the Nilson Report, global card fraud losses exceeded $33 billion in 2022 and are projected to surpass $38 billion by 2027. By 2026, attackers will be leveraging AI-powered phishing, automated credential stuffing, and increasingly automated attack toolkits to breach payment environments that aren’t built for this era of threats.
If your organisation handles cardholder data — whether you’re a merchant, payment processor, or service provider — what you build into your security infrastructure today will determine whether you pass your next audit and, more importantly, whether you suffer a breach. This article cuts through the noise and gives you the exact controls you need to implement, common gaps that get companies fined or flagged, and real-world examples of what happens when organisations get it right — and wrong.
What Are PCI DSS Controls?
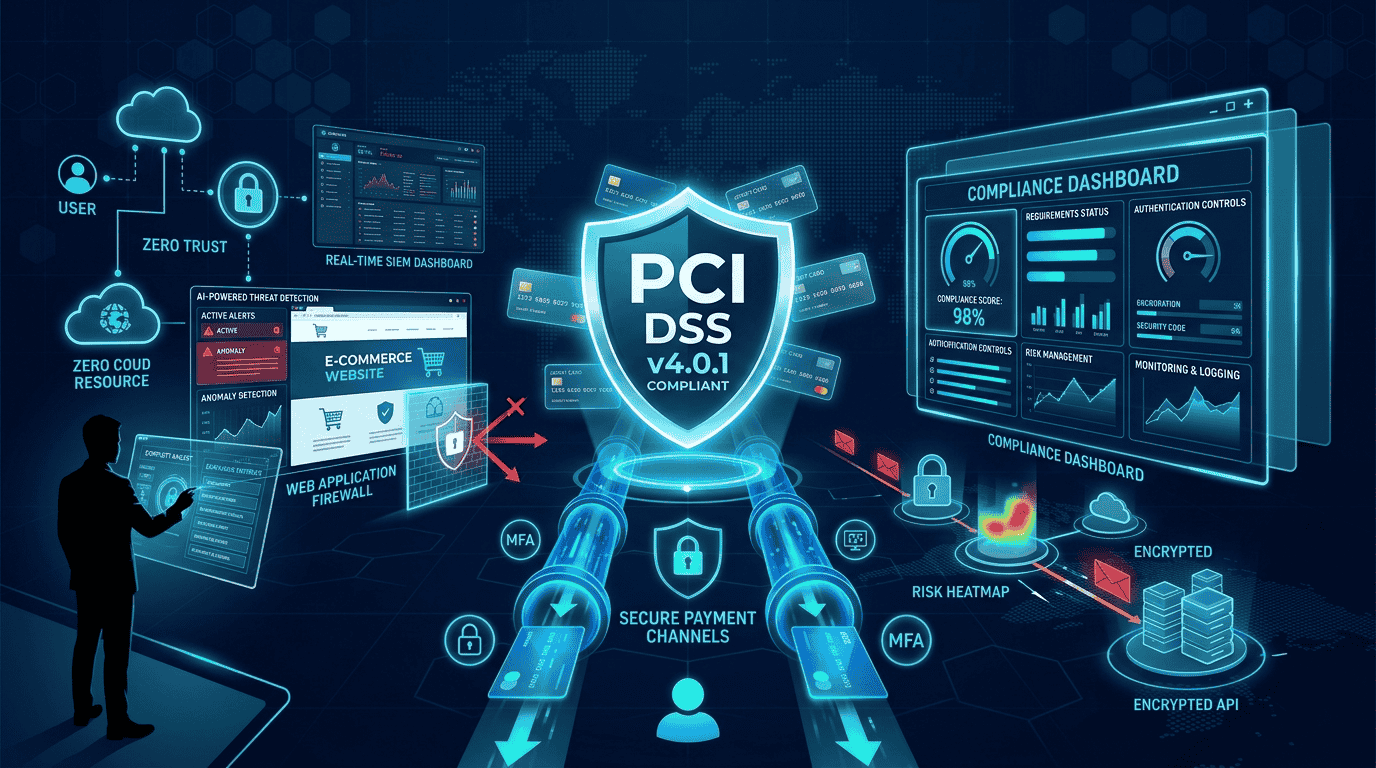
PCI DSS controls are the specific, mandatory security actions your organisation must have in place to protect cardholder data. They cover everything from how you segment your network and authenticate users, to how you encrypt stored card numbers and respond when something goes wrong.
The PCI DSS v4.0.1 framework organises these into 12 requirements grouped across six core security goals. Unlike older versions, PCI DSS 4.0.1 allows a customised approach — meaning organisations operating in complex cloud or hybrid environments can propose alternative controls, provided they can prove those controls meet or exceed the standard’s security objectives. Most organisations, however, still implement the defined requirements, and that’s where the real work happens.
| 📌 Important: 51 New Requirements Now Mandatory (March 2025)
51 new PCI DSS v4.0.1 requirements that were classified as best practices became fully mandatory as of March 31, 2025. Key additions include: payment page script integrity monitoring (Req. 6.4.3), HTTP header security controls (Req. 6.3.3), and expanded MFA requirements. If you assessed under v4.0 before this date, verify your compliance posture against these now-enforceable controls before your next audit. |

7 Key PCI DSS Controls You Must Implement in 2026
1. Network Security Controls
Firewalls, micro-segmentation, default-deny traffic rules, and lateral movement prevention form the outer shell of your PCI environment. Every cardholder data environment (CDE) must be isolated — not just on paper, but enforced at the packet level. Vendors like Fortinet, Palo Alto Networks, and Check Point provide the tooling, but configuration discipline is what actually keeps attackers out.
2. Access Control & Multi-Factor Authentication
Requirement 8.4.2 mandates MFA for all personnel accessing the CDE from outside its network boundary. Requirement 8.4.3 mandates MFA for all remote access to the CDE. Internal LAN access to in-scope systems does not universally require MFA under the defined approach — though it is strongly recommended under defence-in-depth. Role-based access, least-privilege enforcement, and unique user IDs are non-negotiable regardless of access method. Privileged access must be monitored in real-time. Shared accounts and standing admin access are audit red flags that regularly cause compliance failures.
3. Cardholder Data Protection (Encryption & Tokenization)
The simplest way to protect card data is to not store it. Where storage is unavoidable, AES-256 encryption and robust key management are required. Tokenization replaces sensitive PAN data with non-sensitive tokens and can significantly reduce your compliance scope — but only when implemented correctly. The token vault, key management system, and any system capable of de-tokenizing must still be considered in-scope. Refer to the PCI SSC Tokenization Product Security Guidelines when evaluating solutions. Organisations that store card data in plaintext — even temporarily in logs or databases — are consistently the ones making breach headlines
| ⛔ Critical: SAD Storage Prohibition (Req. 3.3.1)
PCI DSS Requirement 3.3.1 absolutely prohibits storing Sensitive Authentication Data (SAD) — including CVV2/CVC2 codes, full magnetic stripe data, and PINs — after transaction authorisation, even in encrypted form. This applies to all entities including issuers. Developers must audit all transaction logs, error logs, and debug files for accidental SAD retention. This is one of the most commonly violated PCI requirements. |
| 📌 Real-World Example: Target Data Breach (2013) — Still Relevant Today
Target’s breach exposed 40 million payment card records. Attackers gained initial access through stolen credentials from a third-party HVAC vendor — the exact third-party risk vector that PCI DSS Requirement 12.8 is designed to control. Malware then scraped card data from POS system memory before encryption could occur, because point-of-sale systems lacked proper segmentation and cardholder data wasn’t tokenized at the endpoint. The same attack pattern is still used today. The lesson: encryption controls must cover data in transit, at rest, and in memory — and third-party access must be tightly scoped and monitored. |
4. Logging, Monitoring & SIEM Integration
Collecting logs without actively reviewing them is one of the most common PCI failure points. PCI DSS requires centralized log management, daily log review, real-time alerting, and File Integrity Monitoring (FIM). A properly configured SIEM doesn’t just satisfy auditors — it’s how you catch attacks before they become breaches. Automated alerting on anomalous behavior, failed logins, and configuration changes should be standard, not optional.
5. Vulnerability Management & Patch Discipline
Quarterly external vulnerability scans, internal scans after any significant change, critical patch deployment within 30 days, and annual penetration testing — these aren’t suggestions, they’re requirements. CISA data shows that high-severity CVEs are frequently weaponised within 24–72 hours of public disclosure. For critical vulnerabilities in payment-adjacent systems, the 30-day patching window permitted by PCI DSS is increasingly a risk acceptance decision, not a safety margin. Organisations that treat patching as a routine calendar event are already running behind the threat curve.
6. Secure Software Development (SDLC Controls)
Payment applications must be built with security from the first line of code. PCI DSS requires secure coding standards, peer code reviews, SAST (static analysis) and DAST (dynamic testing), and controlled change management. Any application that touches cardholder data and was built without these controls should be treated as a liability until it has been properly assessed.
7. Incident Response & Business Continuity
An incident response plan that hasn’t been tested is just a document. PCI DSS requires annual IR plan reviews, clearly defined roles, tabletop exercises, and tested backup and recovery procedures. When a breach occurs — and statistically, it will — how quickly you contain it determines the scale of the damage, the regulatory exposure, and whether you keep your ability to process card payments.
8. Third-Party & Supply Chain Risk Controls (Req. 12.8 / 12.9)
Every third-party service provider with access to cardholder data must have a formal written agreement acknowledging their PCI DSS responsibilities (Req. 12.8.2). Organisations must maintain a list of all such providers, monitor their compliance status, and obtain annual evidence of their own PCI DSS compliance — via Report on Compliance (RoC), Attestation of Compliance (AOC), or applicable SAQ. Responsibility matrices must clearly document which controls each party owns. This is one of the most under-managed areas in PCI assessments and one of the most common breach entry points.
5 Common PCI DSS Implementation Gaps (That Get Companies Failed)
According to the Verizon Data Breach Investigations Report and recurring findings across PCI DSS assessment engagements, these failure patterns appear consistently:
- Undefined or bloated scope — organisations fail to accurately identify which systems touch cardholder data, either missing critical in-scope components or failing to properly segment them.
- Missing or inconsistent MFA — privileged accounts without multi-factor authentication remain the single most common access control finding.
- Encryption without key management — card data is technically encrypted, but encryption keys are stored insecurely, rotated infrequently, or accessible to too many people.
- Logs collected, never reviewed — SIEM dashboards look impressive, but no one is acting on alerts or conducting the mandatory daily log reviews.
Third-party vendors with unchecked access — service providers and technology partners with access to the CDE are not adequately monitored, scoped, or reviewed.
| 📌 Real-World Example: British Airways ICO Fine (2020) — A Monitoring & Third-Party Failure
British Airways was fined £20 million by the UK’s Information Commissioner’s Office (ICO) under UK GDPR — not a PCI DSS fine (PCI DSS fines from card brands are not publicly disclosed). Attackers used a third-party script injected into their payment page to skim card data for over two months, completely undetected. The breach exploited weak monitoring controls and insufficient third-party vendor oversight — both core PCI DSS requirements. Over 400,000 customer card details were compromised. The incident is a textbook case for why logging, monitoring, and vendor management controls aren’t just compliance items — they’re what actually stop attacks. |

Frequently Asked Questions
Q: What’s the difference between PCI DSS 4.0 and 4.0.1?
A: PCI DSS v4.0 was officially retired on December 31, 2024. All assessments must now use v4.0.1. The requirement changes are minor clarifications, but organisations should formally review their control mappings and update their RoC/SAQ documentation to the v4.0.1 templates. Any controls that were best practices under v4.0 but became mandatory on March 31, 2025 must now be implemented.
Q: How often do PCI DSS controls need to be tested?
A: Core controls require continuous monitoring, quarterly vulnerability scans, and annual penetration testing. Certain controls — like log reviews and access audits — must be performed daily or monthly, meaning PCI compliance is an ongoing operational discipline, not an annual event.
Q: Can cloud-hosted environments achieve PCI DSS compliance?
A: Yes — cloud environments can be PCI DSS compliant, but scope definition becomes significantly more complex. Your cloud provider’s compliance certifications cover their infrastructure; you’re still responsible for how you configure, monitor, and protect what runs on top of it.
Q: When should we use the Customised Approach instead of Defined Requirements?
A: Use the Customised Approach only when your environment makes standard controls genuinely infeasible — not as a shortcut. It requires documented risk analysis, thorough testing evidence, and full QSA agreement that your alternative control meets the same security objective.
Q: What SAQ type applies to my organisation?
A: Which PCI DSS controls apply depends on your merchant level and how you accept card payments. Merchants using fully redirected payment pages (SAQ A) face far fewer requirements than those processing card data directly (SAQ D). If you’re unsure which SAQ applies, a scoping conversation with a QSA should be your first step — a wrong SAQ selection invalidates your entire compliance programme.
Final Takeaway
PCI DSS controls are the mandatory security baseline — but the organisations that actually avoid breaches treat them as a floor, not a ceiling. The organisations that pass their assessments confidently and avoid breaches aren’t just following the checklist; they’ve built the controls deeply into how their environments actually work, day to day.
Network segmentation, correctly-scoped MFA, real encryption with SAD controls, active monitoring, disciplined patching, secure development, tested incident response, and third-party governance — these controls, implemented correctly, give you something no audit checklist alone can provide: a payment environment that can actually withstand a modern attack.
Narendra Sahoo (PCI QPA, PCI QSA, PCI SSF ASSESSOR, CISSP, CISA, CRISC, 27001 LA) is the Founder and Director of VISTA InfoSec, a global Information Security Consulting firm, based in the US, Singapore & India. Mr. Sahoo holds more than 25 years of experience in the IT Industry, with expertise in Information Risk Consulting, Assessment, & Compliance services. VISTA InfoSec specializes in Information Security audit, consulting and certification services which include GDPR, HIPAA, CCPA, NESA, MAS-TRM, PCI DSS Compliance & Audit, PCI PIN, SOC2 Compliance & Audit, PDPA, PDPB to name a few. The company has for years (since 2004) worked with organizations across the globe to address the Regulatory and Information Security challenges in their industry. VISTA InfoSec has been instrumental in helping top multinational companies achieve compliance and secure their IT infrastructure.